Introducing the first BIOS-based technology for endpoint security
Learn more about BIOS-SHIELD™ technology at www.bios-shield.com
Many of today's security solutions are based on operating system resources or add-on security apps that are designed to detect and block intrusions by monitoring network traffic — which may be limiting their effectiveness.
At Janus Technologies, we've turned our attention to the endpoints in today's computing environments. Our solution is designed to help protect organizations from ever-evolving threats to sensitive data and to monitor user activity on all computers inside the organization. It offers IT administrators an innovative approach to monitoring, enforcing and analyzing endpoint behavior at the BIOS level, so they can monitor user activity, encrypt data, analyze network activity and discover patterns and unusual activity.
Protection that meets today’s most critical needs
The Janus Secure Computing Platform is specifically designed to help you tackle three of today’s most urgent security problems, offering:
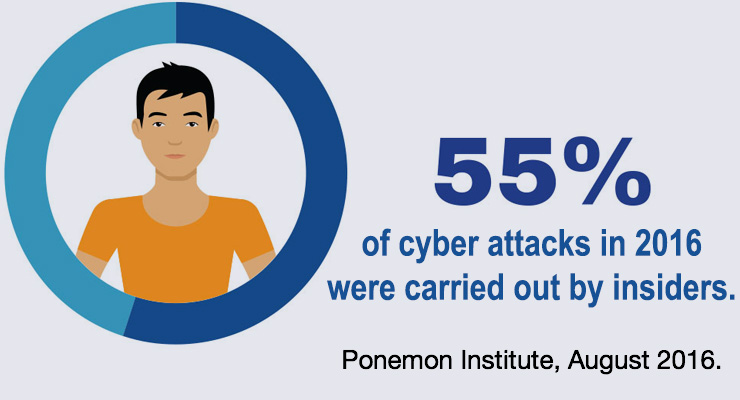
Protection against insider threats
- A BIOS-based layer of security below the operating system on the endpoint enables a virtually tamper-proof solution.
- An intrusion detection system, geo positioning and encryption capabilities offer a layered defense—to help ensure security and convenience.
- BIOS-based protection extends to peripheral devices, including external drives, mice, keyboards, monitors and hard drives.
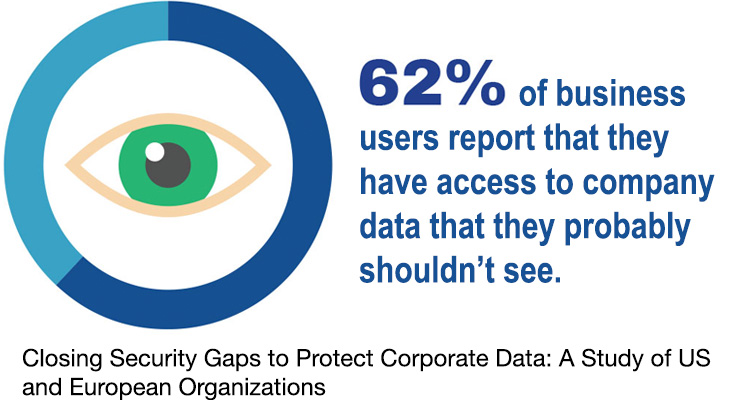
Support for meeting and exceeding compliance mandates
- Built-in flexibility makes it easy to adapt to specific regulatory and other security policy compliance requirements and exceptions—without impacting user productivity.
- Configurable real time monitoring and recording of all device and user activity offers easy access to audit trails and evidentiary reporting information.
- Physical separation of internal and external network connections—via dual operating systems—simulates physical isolation, enabling easier compliance-related monitoring.
Extended security for legacy platforms
- Organizations with multiple install bases running legacy operating systems can deploy and retain a single security platform when they upgrade to a newer system.
- Physical separation of internal and external network connections protects against “importing” malware via copy- and-paste operations.
- Operating system updates and restoration retain all user data and minimize both user downtime and IT personnel involvement.